NHI Threat Detection & Response

The Solution
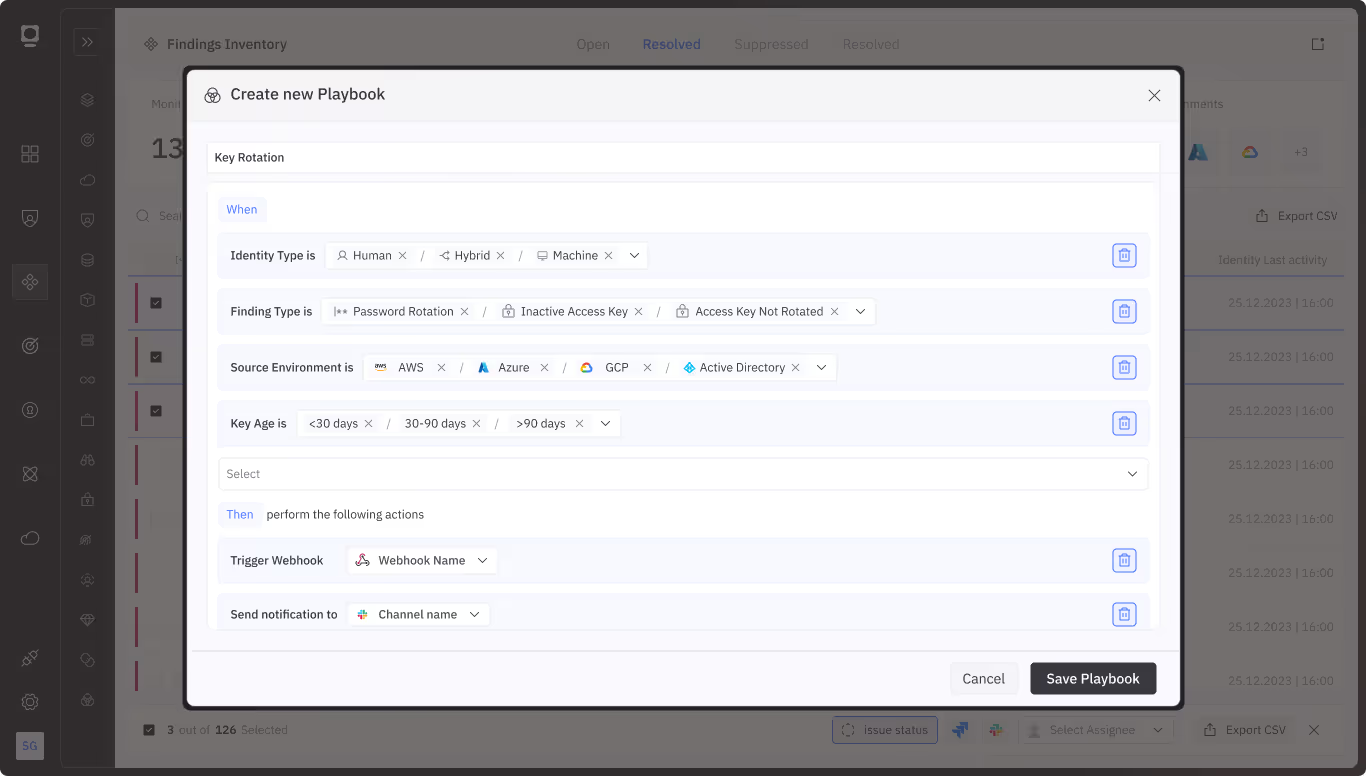
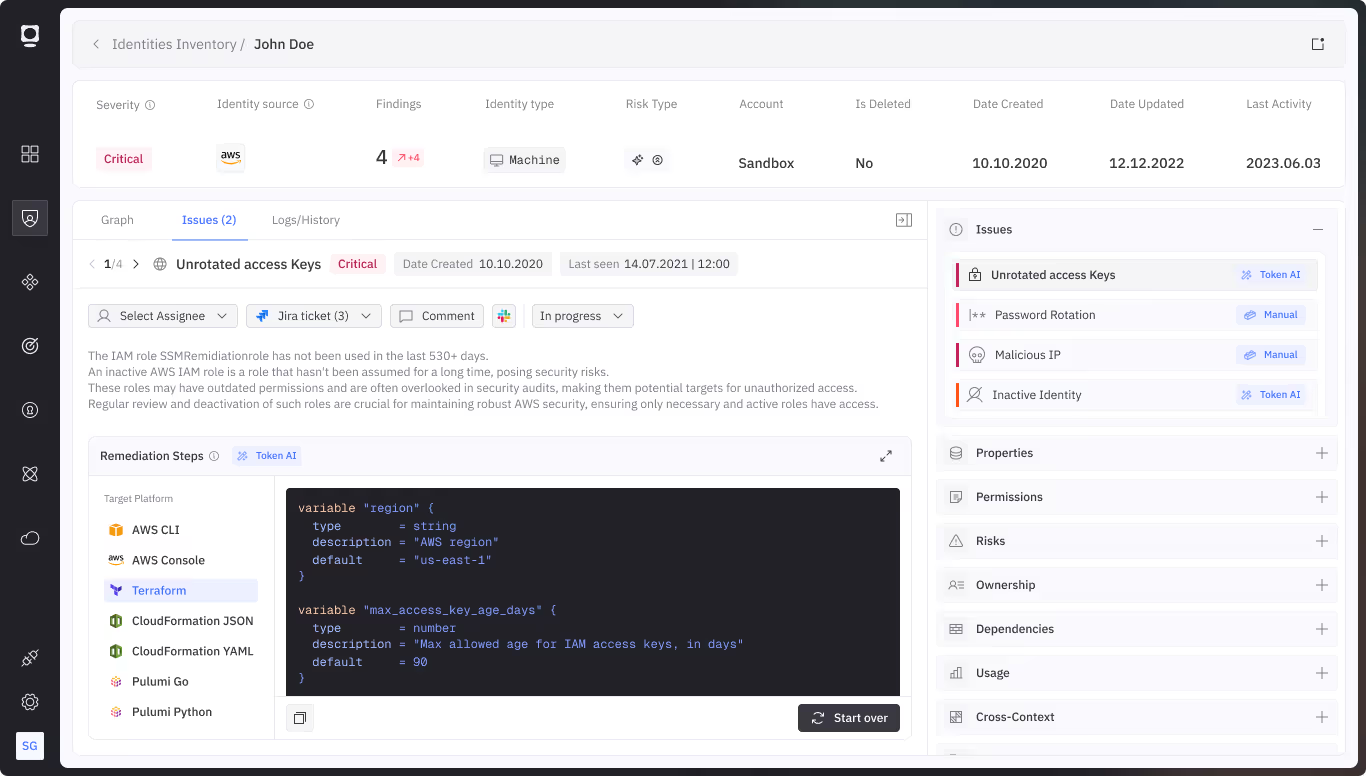
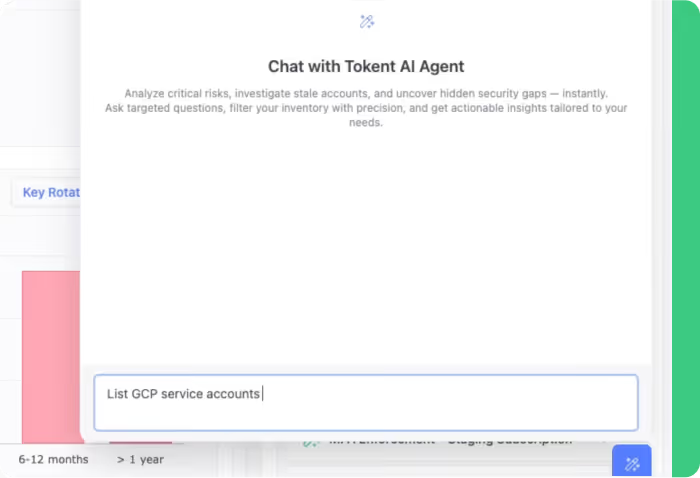
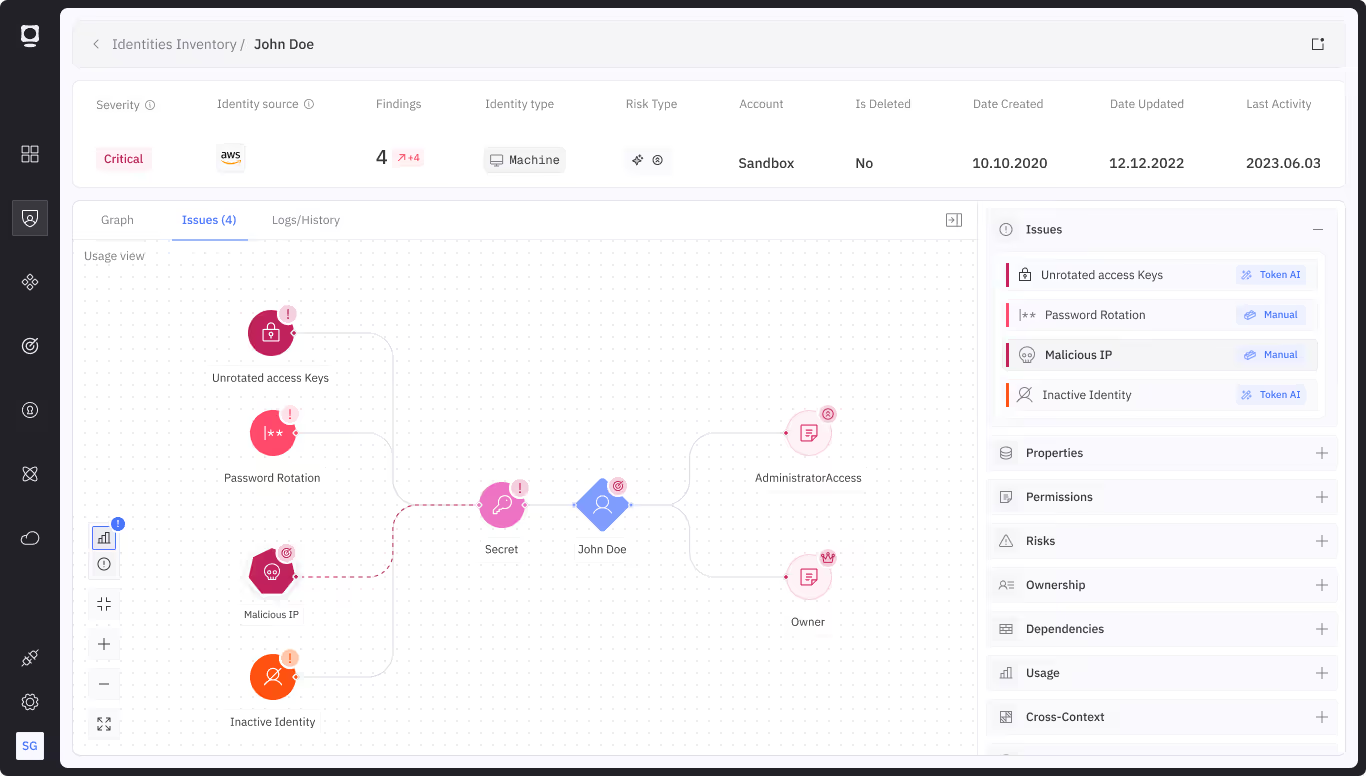
Effective threat detection and response for non-human identities involves real-time monitoring of access attempts, behavioral anomalies, and suspicious activities. Token analyzes behavioral signals, privilege misuse, and credential misuse to surface real-time threats targeting machine identities, enabling immediate, automated response.
Capabilities




Discover other use cases

NHI Discovery and Visibility Across Cloud and AI Agents
Learn More
NHI Security Posture Management
Learn More
NHI Lifecycle Management
Learn More
.gif)