Every AI Agent Needs Access.
We Lock It Down.
Token Security gives you real-time visibility, control, and governance over every AI agent and machine identity across your environment, so you can move fast and stay secure.
Unseen. Unsecured. Out of Control.
As AI use explodes, enterprises face a new class of identity threat: intelligent, autonomous agents with unchecked access to critical systems. These agents connect using identities that are:

Everywhere & Exploding
AI Agent and other Non-Human Identities (NHIs) span across on-prem, cloud, and AI ecosystems, while outnumbering human identities by 45:1.

Complex & Connected
A single compromised agent can trigger cascading damage across every connected system it touches.

Impossible to Remediate
Without understanding context and usage of each AI agent and identity, security and IAM teams fear breaking production systems.
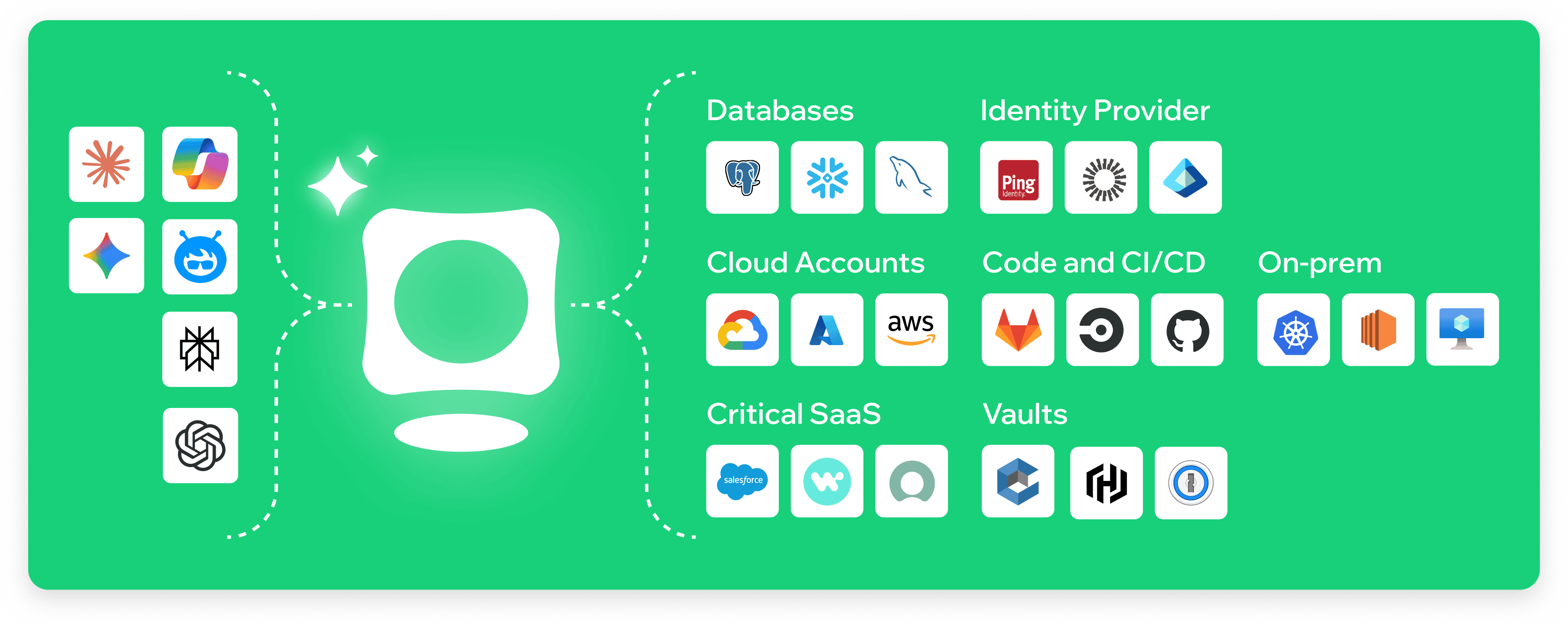
Identity-First AI Security
Token Security’s AI Agent Identity Lifecycle Management capabilities empower enterprises to discover, control, and govern AI agents, while accelerating secure agentic AI adoption.
.png)
.jpg)
A machine-first, AI-native approach
Token Security secures every non-human identity — from service accounts and API tokens to AI agents — with continuous discovery, control, and automated response.
Continuous Discovery & Contextual Visibility
Uncover every AI agent and NHI across on-prem, hybrid, and cloud environments.

Lifecycle Management
Enforce ownership and decommission orphaned identities automatically.

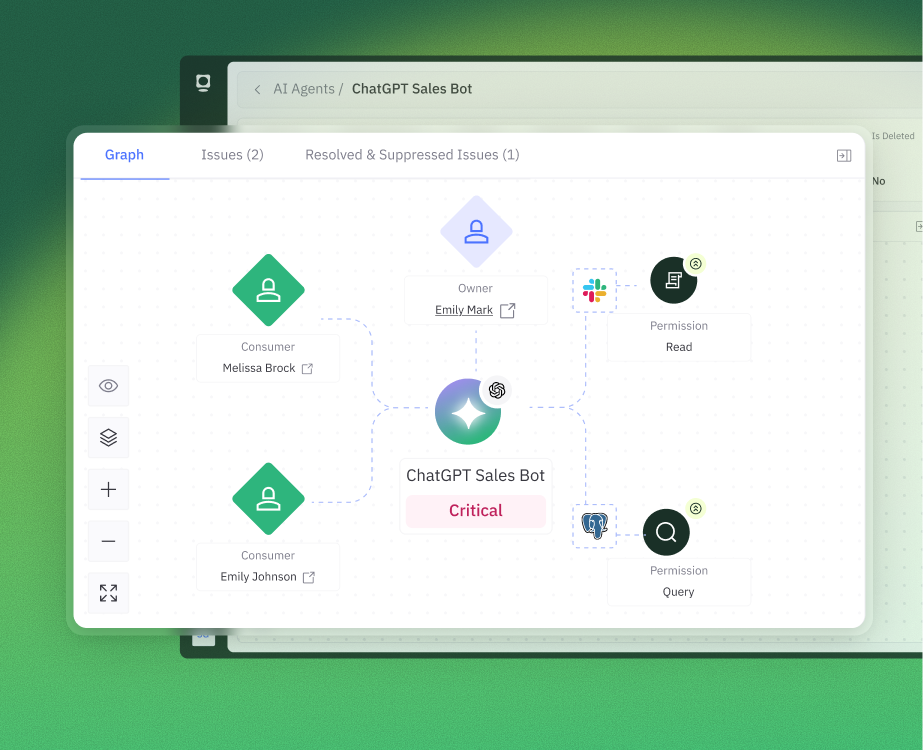
Security Posture Management
Identify permissions drift, right-size access, and eliminate dangerous overexposure.
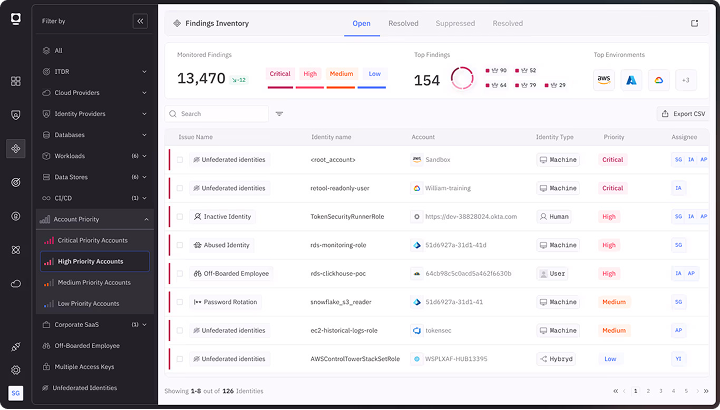
Identity Threat Detection & Response
Detect behavioral anomalies and suspicious activities to respond as they happen.

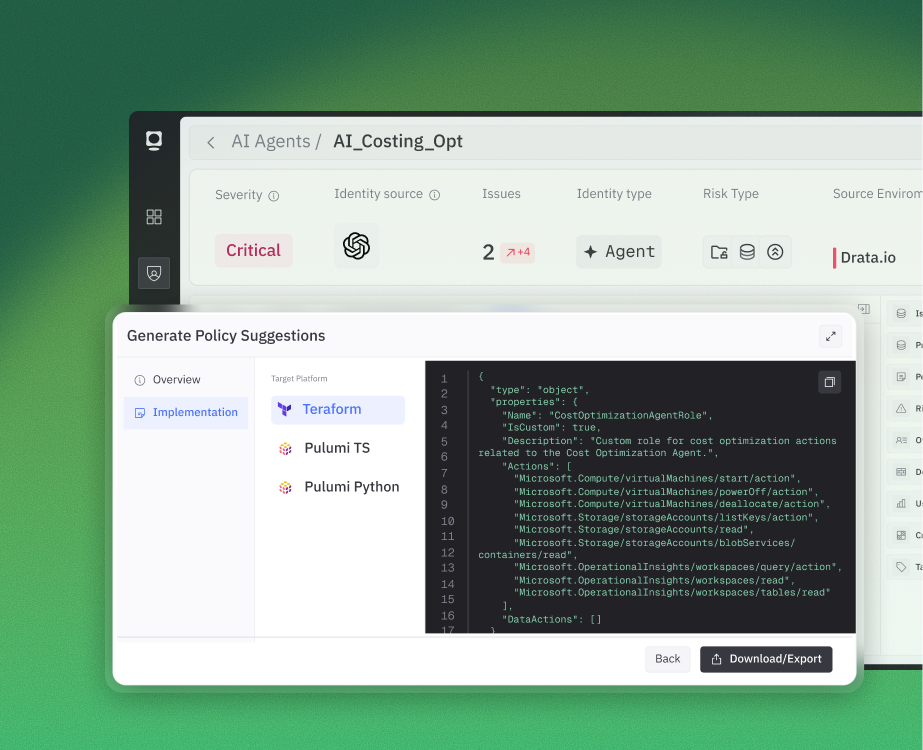
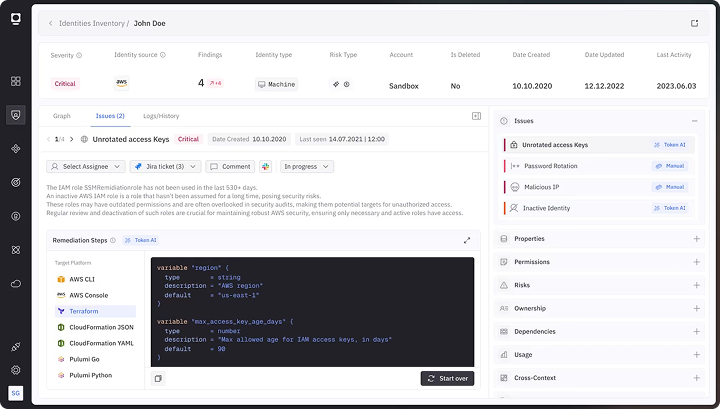
AI-Driven Automation & Remediation
Trigger intelligent remediation workflows based on dynamic risk thresholds and contextual awareness.
Why Token Security
Where others stop at visibility, Token Security delivers full-spectrum Identity Governance to empower enterprises to adopt AI with confidence. What sets us apart:
Context-Aware Intelligence
Understand how agents, identities, and systems connect so you can remediate risk with precision.
End-to-End Lifecycle Control
Manage identities from creation to retirement.
Automated, Scalable Remediation
Remediate faster with AI-generated fixes and auto-enforced playbooks.
Integrated Privilege Governance
Apply least privilege, just-in-time access, and continuous policy enforcement.
Real-Time Threat Response
Neutralize compromised or misbehaving AI agents in seconds.
AI-Native, Real-World Outcomes
The Token MCP Server and AI Agent deliver a real-time natural language interface that lets security teams interact directly with their environment.

The Token MCP Server
Designed to be consumed from your tool of choice, the Token MCP Server enables you to ask questions from your favorite chat application (e.g., Claude, ChatGPT, Gemini) or AI Agent-based application (e.g., Cursor).

The Token AI Agent
Built directly into the Token Security Platform, the Token AI agent gives you native conversational AI capabilities right from the Token UI.
.gif)
.svg)


.png)
















-p-500.png)
-p-500.png)